Software Tools for Cryptographic Inventory
Discover cryptographic risks before they become a threat
An efficient transition to post-quantum cryptography (PQC) begins with a perfect overview.
Manually mapping ciphers in large-scale systems is practically impossible – that is why we have developed a suite of specialized tools that automate data collection and visualize the state of your cryptographic infrastructure.

Creating a Cryptographic Bill of Materials CBOM
The cornerstone of migration is the creation of a so-called CBOM (Cryptography Bill of Materials).
It is a standardized inventory of all encryption algorithms, keys, and libraries used by your applications.
Currently, CBOM is becoming an essential basis for ensuring compliance with the DORA regulation. For financial institutions and their suppliers, it represents key evidence of cyber resilience and the ability to manage risks effectively.
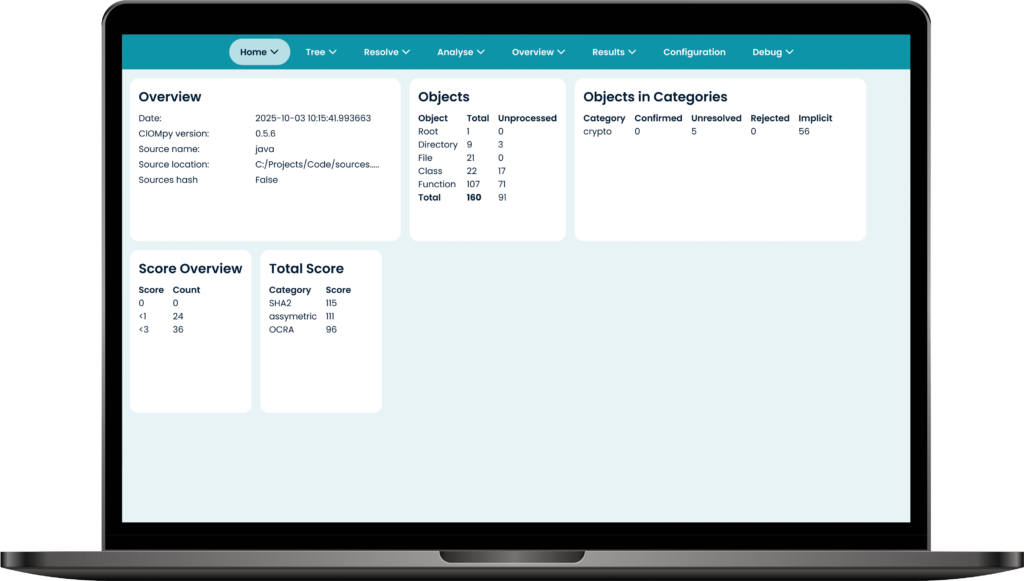
Monet+ CBOMpy
Our key tool for static analysis of source code and configuration files.
It serves for the automatic identification of cryptographic primitives across your software and their convenient manual evaluation.
Automatically searches for the use of cryptography in code.
The tool remembers your manual decisions, thereby accelerating every subsequent analysis.
Generates standardized JSON output ready for further automation.
From core languages (Java, .NET, Python) to mobile platforms (Kotlin, Swift, Dart).
CORE
Demo version
Features:
- Language-independent analysis
- Visualization of findings
STANDARD
Advanced Features
Standard includes:
- All mainstream programming languages
- Save/Load Functionality
- Data import from archives
- JSON CBOM output file
PROFESSIONAL
The most powerful solution
Professional includes:
- All mainstream programming languages
- Save/Load Functionality
- Data import from archives
- JSON CBOM output file
- Automation (CI/CD Pipelines)
- Direct IDE Integration
Validation and Expert Data Enrichment
While automated tools collect data, their context is key for strategic decision-making. This step serves for the authorized evaluation of the state of cryptography and its compliance with security policies.

MONET+ C-Insight
Our proprietary tool for smart editing and management of CBOM files.
It allows specialists to conveniently browse identified cryptographic primitives and add parameters that an automatic scan cannot capture.
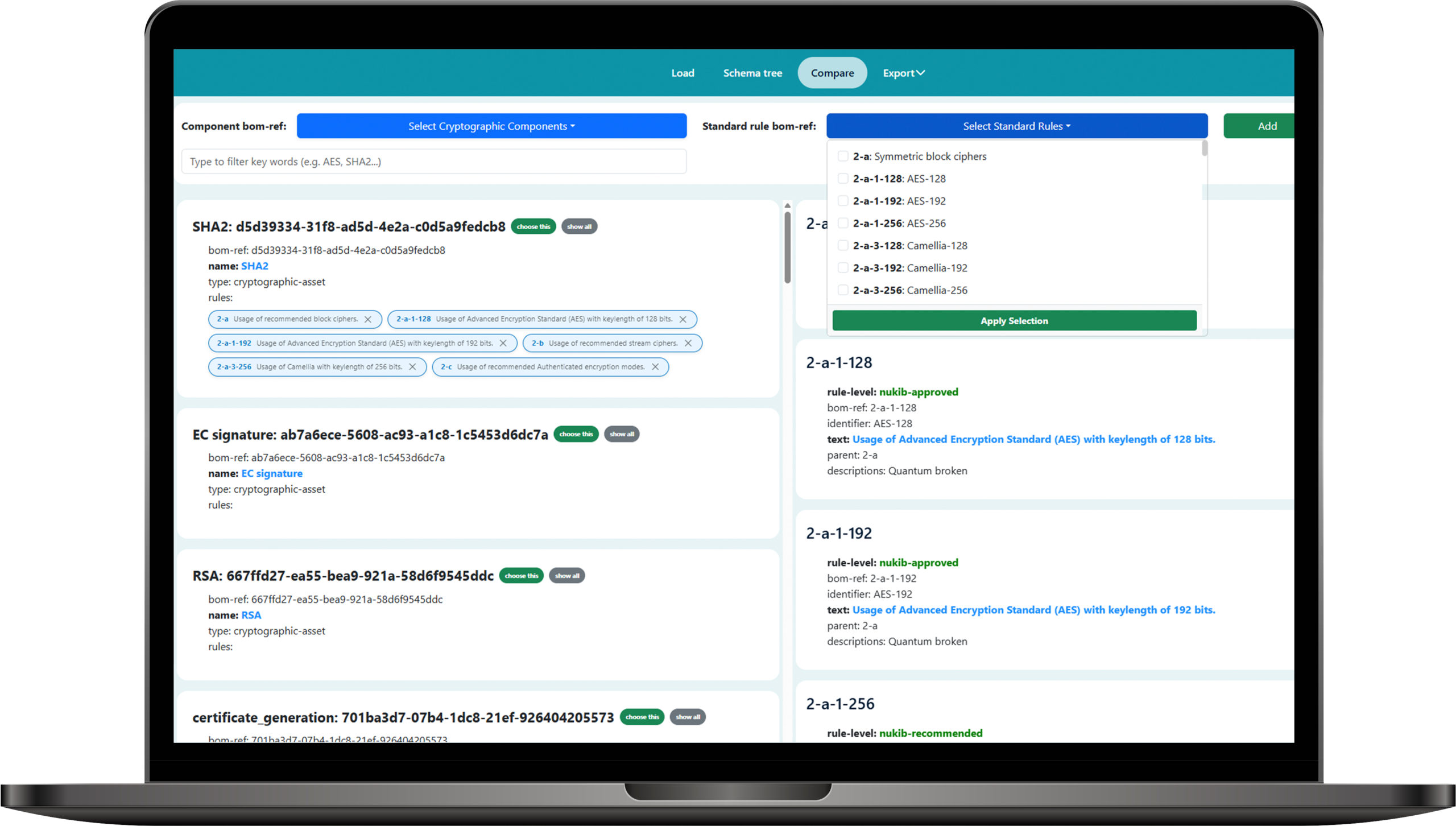
Performing manual and automated verification of whether the used cipher complies with selected standards (e.g., recommendations from NÚKIB, BSI, ENISA, NIST, or internal guidelines), which are uploaded to MONET+ C-Insight in JSON SBOM format.
Clear labeling and mapping of the resistance of individual algorithms to quantum threats for easy prioritization of migration.
Convenient browsing and adding of parameters in complex JSON structures without the need for direct code editing.
Generates a detailed file in JSON CBOM format, which maintains the full context of the cryptographic inventory and serves as the final basis for visualization and management reports.
Threat Visualization and Compliance Control
The final step of the process is the transformation of technical data into a clear picture. Visualization allows security managers and auditors to immediately identify weak spots and track progress in infrastructure security.

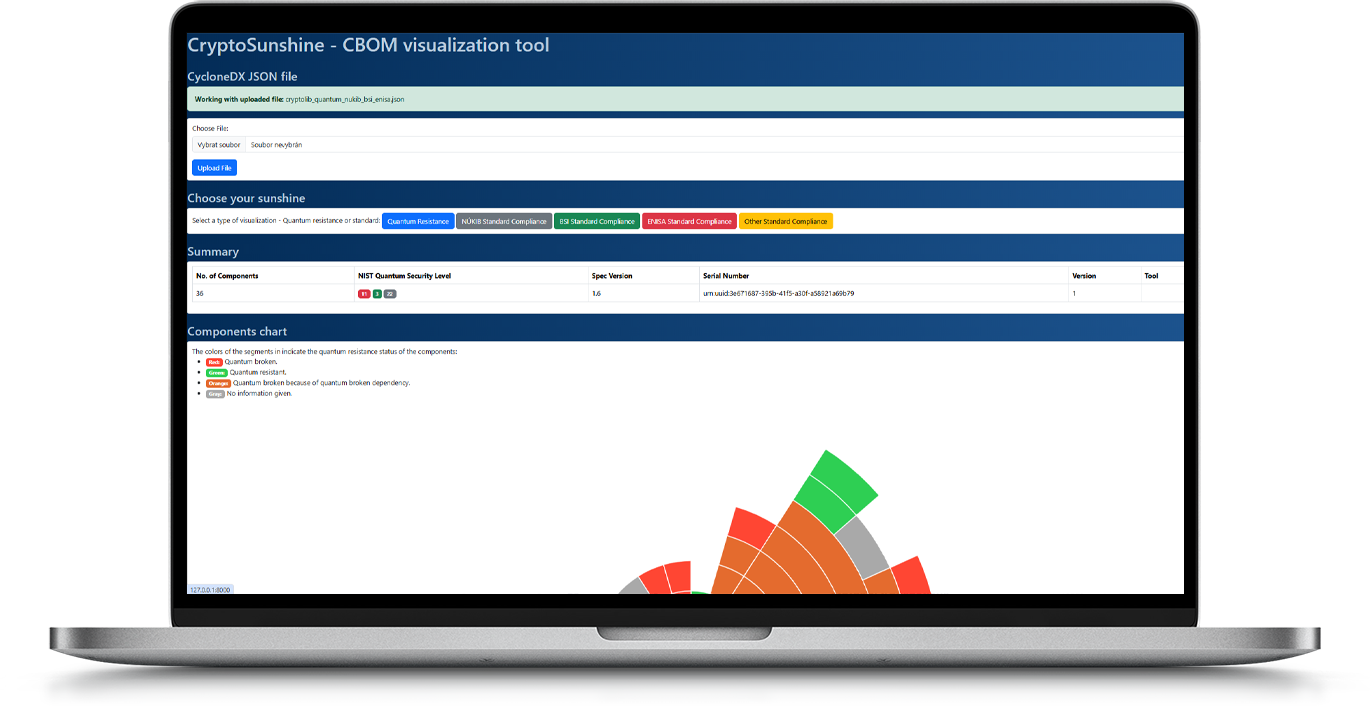
MONET+ CryptoSunshine
Our open-source tool for comprehensive visualization of the cryptographic inventory.
It serves for the clear interpretation of data and the verification of compliance with recommendations from national and international authorities.
MONET+ CryptoSunshine is an extension of the open-source tool Sunshine, developed under the OWASP CycloneDX umbrella and provided under the Apache 2.0 license, which guarantees maximum trustworthiness.
Automatically highlights algorithms that are vulnerable to quantum computers and identifies primitives dependent on them.
Natively displays (non-)compliance with cryptographic standards from NÚKIB, BSI, and ENISA and allows the import of custom internal standards in JSON format.
Offers a human-friendly display of complex relationships within the cryptographic inventory, understandable for both technicians and management.
Identifying ciphers using our tools is the first step on the journey toward future security. Inventory data is your map; we will help you find the safest path to your destination. Explore how your organization can become quantum-resilient.
